By Christian Calvo
Abstract
Bluetooth Low Energy (BLE) is a wireless communication protocol designed for use in a variety of commercial devices. Devices that utilize BLE often have inferior security systems compared to alternative wireless devices, enabling malicious parties to more effectively execute adversarial attacks. To iterate the impact of adversarial attacks on BLE systems, vulnerabilities in these devices and how knowledge of these flaws can be leveraged to cause harm will be evaluated. By addressing the resources available to developers for creation of BLE protocols, the limitations of BLE connections that contribute to their vulnerability to attacks will be identified. Fortunately, security features exist to protect against malicious attacks, thereby minimizing BLE vulnerabilities. Continuing integration of wireless devices in people’s everyday lives makes understanding and addressing their potential security risks essential for ensuring data privacy. Therefore, this analysis aims to educate individuals on the weaknesses and security threats of devices that utilize BLE and how one can shield their device from future adversarial attacks.
Introducing Bluetooth Low Energy
Bluetooth Low Energy (BLE) is a low-power radio that streams data over 40 channels in the 2.4 GHz unlicensed industrial, scientific, and medical (ISM) frequency band. BLE was developed to enable wireless communication with low power consumption, making it ideal for battery-powered devices like wearables, sensors, and IoT devices that require long battery life and infrequent data transmission.
BLE was introduced in 2009 as a part of Bluetooth 4.0 and is a modified version of Bluetooth classic. BLE was designed to have low power consumption, provide low latency, and operate in short-range.[1] Since Bluetooth 4.0, BLE has seen several updates and now supports data transfer speeds up to 2 Mbps, longer range of up to 240 meters, and communication capabilities such as point-to-point, broadcast, and mesh, enabling developers to communicate between two devices or create a network.
A BLE connection is established using one of three advertising channels. During the connection setup multiple connection-specific parameters are exchanged between devices. These include the used hopping sequence, access address (AA), hopping interval, etc.[2] A connection itself consists of a sequence of connection events. During a connection event the two devices exchange messages on one physical channel. In between each connection event the two devices hop to the next channel based on the hopping sequence. Every packet sent starts with a preamble and a connection specific AA. Both are essential for determining the start of a valid packet.[3] These connection parameters are transmitted only during the initial connection setup. Attackers eavesdrop them when a connection is being established or reverse engineer them. Since BLE often operates in public, unencrypted airwaves, connections are susceptible to many forms of attacks.
This puts your information, your devices, and you at risk. As the world becomes ever more online and interconnected, the dangers these technologies pose grow. For example, take the remote features of the Tesla cars, if someone hacked your Tesla, locked the physical controls, and used its self-driving features to send it to their location. BLE was built to be a low-cost, low latency variant of Bluetooth Classic. It is intended mostly for short-distance connections and this led to security becoming an afterthought in its development. However, as it has become far more commonplace this is creating gaps in our device’s security. Attempts have been made to close these gaps, but they still exist.
Vulnerabilities
Over the years, publications have brought to light vulnerabilities in BLE.
In 2019 Celosia et al. showed how a Generic ATTribute Profile (GATT) can be leveraged to create a fingerprint that can be exploited to track user devices with anti-tracking features. This flaw exists since services exposed by a server are presented in a GATT profile and many of these, including the System ID, are defined by the Bluetooth SIG. So, if an adversary connects to the device, they can query these services and characteristics and use them to calculate a fingerprint.[4]
In 2019 Martin et al. showed that it is possible to track user activity, such as using certain setting pages, screen unlocking and locking, and answering phone calls. This was demonstrated by capturing advertising packets sent during Apple Continuity actions.[5]
The pairing method of Bluetooth 4.0 called legacy pairing was found to be vulnerable to offline brute force attacks, where an attacker systematically attempts all possible passkey combinations until the correct one is found.[6] This is due to the fact that an attacker who is able to eavesdrop on the pairing procedure only needs to discover the passkey and keys used in legacy pairing only have 6 decimal digits of entropy.
In 2020 Claverie and Lopes-Esteves, noted that the use of the key hierarchy method reduces the number of possible keys to 216. This means that when a device pairs with a lot of devices there is a high probability that two devices will derive the same key.[7] The root of this issue is the low diversification of generated keys. So, if an attacker has access to a vulnerable device for long enough, the attacker can pair with it multiple times and enumerate all possible keys. This would allow an attacker to decrypt all past and future connections for this device.[8]
In the association model negotiation(authentication) phase, the devices choose one of the modes out-of-band (OOB), just-works (JW), numeric comparison (NC), or passkey-entry (PE) based on their security requirements and I/O capabilities.[9] However, the exchanged capabilities aren’t authenticated. This means an attacker can intercept and modify BLE pairing messages to downgrade the security mode. For example, when you pair a phone to your car you normally need to verify a number (NC) but using this vulnerability an attacker can change your car to pair using just works and connect to your car without your knowledge.
Attacks:
Sniffing is an attack where a third-party aims to obtain information communicated between BLE devices. This is typically accomplished through passive eavesdropping but can be done by actively triggering the transmission. Sniffing is one of the most common attacks since it can obtain important information about a BLE connection, such as the hopping sequence, access address, hopping interval, etc. The information obtained in a sniffing attack can then be used to carry out other, more dangerous, attacks. Sniffing attacks take advantage of the fact that BLE connections take place on public channels. The two main forms of sniffing are passive sniffing and active sniffing. Passive sniffing is used to gather information about device activity, identify vulnerabilities, or collect sensitive data.[10] Using active sniffing an attacker can obtain sensitive information exchanged between devices by injecting malicious packets or forcing the devices to re-establish connections.[11]
A Man in the Middle (MITM) attack refers to an attacker relaying, dropping, or manipulating a connection. This BLE attack involves two BLE devices impersonating the two legitimate ones.[12] The legitimate devices will connect to the fake ones and then all messages will be sent first to the fake devices which will then relay the data to the legitimate ones. The fake devices can choose to manipulate the data sent to the legitimate central device after receiving initial data. Additionally, the attacker can also drop the connection between the legitimate devices after the fake devices are connected to.
In 2020 Ray Felch, described his implementation of a relay attack. A relay attack is a form of the MITM attack where an attacker relays information between two legitimate devices without their knowledge. Felch’s relay attack uses Peripheral Device Impersonation to impersonate a KeyWe lock and Central Device Impersonation to impersonate the Victim’s phone. When the Victim’s phone connects to the fake lock the sent packets are logged and passed on to the device which impersonates the Victim’s phone and passes the original packets to the lock.[13] This implementation displays how the vulnerabilities of BLE can be used to gain access to people’s homes.
An Undisputed Advertising Attack is an attack where the attacker causes an Undisputed Advertising condition to change the advertised name of a device on scanning Central Devices. This attack makes use of the caching mechanism of the Central Device.[14] This attack can be used for a MITM attack by poisoning the cache of a Central Device with a name of peripheral device they expect to connect to later. This flaw in the BLE caching mechanism can be used to setup a device near your MacBook that uses a MITM attack to obtain your passkey when you unlock your laptop using Auto Unlock.
In 2019 Christopher Hensler and Patrick Tague published their implementation of this attack, dubbed Bluestaking. Their implementation was tested using an Android phone as the Central Device. When two separate devices advertised under the same address with only one advertising a name, the name persisted even after the named device stopped advertising. This can be used to force a Central Device to identify a beacon or other nameless device with a name set by an attacker.[15] Additionally, this attack does not require the device being impersonated to be in proximity because it utilizes the cache mechanism of the Central Device.
Jamming is an attack where an attacker blocks parts of a BLE communication or an entire connection. BLE jamming can target multiple channels or specific packets or connections.[16] Jamming can be used for several malicious actions, such as denial of service and session hijacking.
Denial of Service (DoS) attacks are a form of jamming where an attacker denies the availability of BLE devices or networks by flooding them with a large amount of malicious traffic or by exploiting vulnerabilities to freeze devices.[17]This type of attack could be used by attackers to disable medical devices. Denial of Service can also be used to shut down BLE functionality within an area since all BLE connections are established in the three advertising channels.
Session Hijacking is an attack that utilizes jamming to take over a device’s role in a BLE connection. Damien Cauquil published an implementation of this attack called BtleJack.[18] An attacker could use this attack to hijack the connection to someone’s pacemaker and kill someone with a single command.
A Disputed Advertising Attack is a BLE attack where an attacker causes a disputed advertising condition to change the discoverability of a device.
In 2019 Christopher Hensler and Patrick Tague demonstrated their implementation of a Disputed Advertising Attack. In their implementation, they had two Raspberry Pis devices with different names advertising the same address and an Android phone served as the Central Device. The “Victim” Pi advertised itself as discoverable and the “Attacker” Pi advertised itself as not discoverable. Before the attack began the “Victim” Pi was detectable, but as soon as the “Attacker” Pi began advertising the “Victim” was no longer discoverable. This caused the “Victim” Pi to be removed from the list of connectable devices on the Android, but once the attack stopped the “Victim” Pi returned to the list.[19] If you had a wireless lock with no physical fallback, then an attacker could disable that device and lock you out of your home.
Tools
The Ubertooth One, created by Michael Ossman in 2011, is an open-source hacking tool. The Ubertooth One was mainly designed for hacking Bluetooth communications, allowing the monitoring of both upcoming and existing connections. The Ubertooth One is a great example of the dangers posed by BLE vulnerabilities because it makes hacking software easy to use. All a hacker with an Ubertooth One needs is some linux terminal experience to execute the built-in hacking commands. The ubertooth-btle command, which was created by Mike Ryan in 2013, is used for sniffing BLE connections, interfering with BLE connections, and sending advertising packets. Sending advertising packets, referred to as faux slave mode, injects advertising packets using a given Bluetooth device address. Faux slave mode is used for creating a fake peripheral device impersonating another peripheral device.
The Flipper Zero is an open-source hacking and penetration testing tool developed by Alex Kulagin and Pavel Zhovner in 2019. The Flipper Zero was designed for hacking and interacting with various types of radio frequency (RF) signals. Hackers have shown that it is capable of executing attacks such as BLE spamming, BadUSB input over BLE, and Erwin Ried created the Mayhem v2 module which enables BLE sniffing. However, the Flipper Zero isn’t as capable of BLE hacking as other tools such as the Ubertooth One.

Mayhem v2 Module attached to Flipper Zero. [Source]
Security Features and Counter Measures:
BLE includes several security features separated into levels and modes. This is intended to make BLE more flexible. The various levels and modes are shown in the table below.
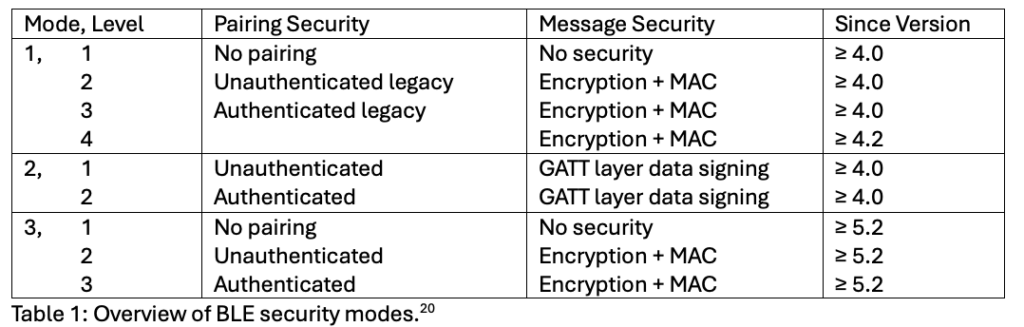
Table 1: Overview of BLE security modes.[20]
Bluetooth 4.0 introduced two security modes. In security mode 1, the connection is encrypted and authenticated using AES128-CCM in all but level 1. However, security mode 1 level 1 provides no security.[21] In security mode 2, the connection is unencrypted, but data is signed using a special key on a higher layer of the BLE protocol in order to authenticate data. Bluetooth 4.0 defines two pairing methods, authenticated and unauthenticated. Authenticated pairing exchanges additional information through an out-of-band channel or through user interaction, this is so that it cannot be eavesdropped by an attacker.[22] Authenticated pairing prevents MITM attacks. For example, when you are pairing your phone to a car it may ask you to verify a code shown on screen. After pairing is performed, the encryption key has been exchanged and the connection can be encrypted using this key. The connection is encrypted using the AES-CCM algorithm.
Recognizing that BLE devices are susceptible to tracking, the Bluetooth SIG introduced several address types to reduce the trackability of devices. These address types are the public address, the static address, the resolvable private address, the non-resolvable private address, and the reconnection address. Bluetooth 4.0 describes this privacy feature only for devices in the peripheral or central role.
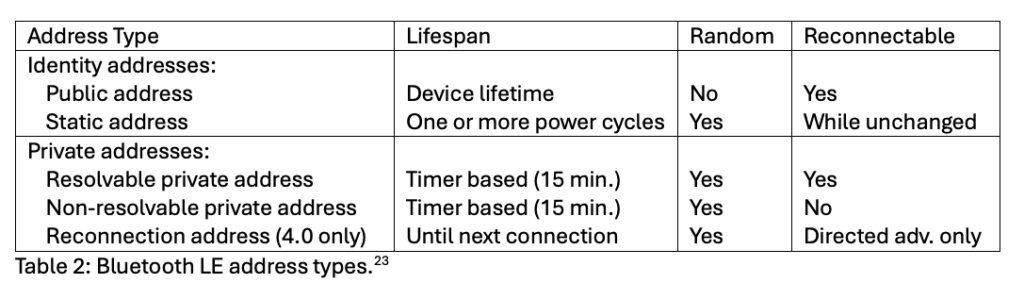
Table 2: Bluetooth LE address types.[23]
Version 4.2 introduced a fourth level for security mode 1, called “Authenticated LE Secure Connections (LE-SC) pairing with encryption” and addresses flaws in the security of Version 4.0. Mode 1, Level 4 was improved in version 5.0 by making a key length of 128 bits mandatory, this prevented KNOB downgrade attacks.[24] LE-SC can also be used to prevent BtleJack attacks.[25]
LE-SC enables both devices to agree on a shared key without transmitting it over the air removing the risk of it being eavesdropped. LE-SC pairing supports four different association models, Just Works (JW), Numeric Comparison (NC), Passkey Entry (PE), and Out-of-Band (OOB). Just Works does not provide any MITM protection. OOB authentication is usable if out-of-band communication is possible in either both directions or only in one direction.[26]
Version 4.2 introduced several privacy functions like the Central Address Resolution characteristic, controller-based RPA generation and resolution, and two privacy modes: device privacy and network privacy mode.[27] In device privacy mode, the device will accept advertising packets containing their identity address or a peer’s private address regardless of prior exchanged Identity Resolving Key (IRK). In network privacy mode, devices are only allowed to accept advertising packets containing private addresses as the device address.
Version 5.2 introduced a new security mode 3 for the new “LE Isochronous Channels”.[28]
In 2024 Zhe Wang published a journal that listed several ways to secure BLE devices.[29] By disabling unused Bluetooth features or services, the attack surface and risk of exploitation can be reduced by removing features that can be used as attack vectors. By using stronger pins and passkeys, brute force attacks can be prevented since stronger keys are harder to exploit. Deploying BLE sniffing detection tools can help detect suspicious or unauthorized access and alert admins to attacks in real time for faster response and mitigation. Using authentication and encryption mechanisms ensures that only authorized devices can connect and that data sent remains confidential and secure. Limiting the range of BLE signals helps mitigate the risk of eavesdropping and unauthorized access.
Conclusion:
BLE revolutionized the world of wireless devices by allowing long-lasting communications with low-power consumption which created a boom in wireless wearables and wireless integrated tools and devices. However, BLE was designed to maximize energy efficiency and lacks robust security. As a result, BLE protocols contain vulnerabilities and design flaws which hackers take advantage of using sniffing, man-in-the-middle attacks, and jamming. The dangers of these attacks are further exacerbated by highly accessible hacking tools like the Ubertooth One and Flipper Zero. As the world becomes ever more connected wirelessly, security becomes an ever more significant concern. To mitigate these concerns, it is necessary for developers to adopt stronger security practices and users must be aware of immediate threats and preventative actions to take.
References:
Matthias Cäsar et al., “A Survey on Bluetooth Low Energy Security and Privacy,” Computer Networks 205 (2022): 108712, https://doi.org/10.1016/j.comnet.2021.108712.
Khalid Hasan et al., “A Comprehensive Review of Wireless Body Area Network,” Journal of Network and Computer Applications 143 (2019): 178–98, https://doi.org/10.1016/j.jnca.2019.06.016.
Ray Felch, “Machine-in-the-Middle (MitM) BLE Attack – Black Hills Information Security.Pdf,” October 28, 2020.
Christopher Hensler and Patrick Tague, “Using Bluetooth Low Energy Spoofing to Dispute Device Details,” Proceedings of the 12th Conference on Security and Privacy in Wireless and Mobile Networks, 2019, 340–42, https://doi.org/10.1145/3317549.3326321.
Guillaume Celosia et al., “Fingerprinting Bluetooth-Low-Energy Devices Based on the Generic Attribute Profile,” Proceedings of the 2nd International ACM Workshop on Security and Privacy for the Internet-of-Things, 2019, 24–31, https://doi.org/10.1145/3338507.3358617.
Jeremy Martin et al., “Handoff All Your Privacy – A Review of Apple’s Bluetooth Low Energy Continuity Protocol,” Proceedings on Privacy Enhancing Technologies 2019, no. 4 (2019): 34–53, https://doi.org/10.2478/popets-2019-0057.
Tristan Claverie and José Lopes-Esteves, “Testing for Weak Key Management in Bluetooth Low Energy Implementations,” 2020, https://www.sstic.org/2020/presentation/testing_for_weak_key_management_in_bluetooth_low_energy_implementations/.
Zhe Wang, “Securing Bluetooth Low Energy: A Literature Review,” ArXiv, 2024, https://doi.org/10.48550/arxiv.2404.16846.
Damien Cauquil, “YOU’D BETTER SECURE YOUR BLE DEVICES OR WE’LL KICK YOUR BUTTS !,” DEF CON 26, August 12, 2018.
Bibliography:
Cäsar, Matthias, Tobias Pawelke, Jan Steffan, and Gabriel Terhorst. “A Survey on Bluetooth Low Energy Security and Privacy.” Computer Networks 205 (2022): 108712. https://doi.org/10.1016/j.comnet.2021.108712.
Cauquil, Damien. “YOU’D BETTER SECURE YOUR BLE DEVICES OR WE’LL KICK YOUR BUTTS !” DEF CON 26, August 12, 2018.
Celosia, Guillaume, Mathieu Cunche, Peng Liu, and Yuqing Zhang. “Fingerprinting Bluetooth-Low-Energy Devices Based on the Generic Attribute Profile.” Proceedings of the 2nd International ACM Workshop on Security and Privacy for the Internet-of-Things, 2019, 24–31. https://doi.org/10.1145/3338507.3358617.
Claverie, Tristan, and José Lopes-Esteves. “Testing for Weak Key Management in Bluetooth Low Energy Implementations,” 2020. https://www.sstic.org/2020/presentation/testing_for_weak_key_management_in_bluetooth_low_energy_implementations/.
Felch, Ray. “Machine-in-the-Middle (MitM) BLE Attack – Black Hills Information Security.Pdf,” October 28, 2020.
Hasan, Khalid, Kamanashis Biswas, Khandakar Ahmed, Nazmus S. Nafi, and Md Saiful Islam. “A Comprehensive Review of Wireless Body Area Network.” Journal of Network and Computer Applications 143 (2019): 178–98. https://doi.org/10.1016/j.jnca.2019.06.016.
Hensler, Christopher, and Patrick Tague. “Using Bluetooth Low Energy Spoofing to Dispute Device Details.” Proceedings of the 12th Conference on Security and Privacy in Wireless and Mobile Networks, 2019, 340–42. https://doi.org/10.1145/3317549.3326321.
Martin, Jeremy, Douglas Alpuche, Kristina Bodeman, Lamont Brown, Ellis Fenske, Lucas Foppe, Travis Mayberry, Erik Rye, Brandon Sipes, and Sam Teplov. “Handoff All Your Privacy – A Review of Apple’s Bluetooth Low Energy Continuity Protocol.” Proceedings on Privacy Enhancing Technologies 2019, no. 4 (2019): 34–53. https://doi.org/10.2478/popets-2019-0057.
Wang, Zhe. “Securing Bluetooth Low Energy: A Literature Review.” ArXiv, 2024.https://doi.org/10.48550/arxiv.2404.16846.
[1] Cäsar et al., “A Survey on Bluetooth Low Energy Security and Privacy.”
[2] Cäsar et al., “A Survey on Bluetooth Low Energy Security and Privacy.”
[3] Cäsar et al., “A Survey on Bluetooth Low Energy Security and Privacy.”
[4] Celosia et al., “Fingerprinting Bluetooth-Low-Energy Devices Based on the Generic Attribute Profile.”
[5] Martin et al., “Handoff All Your Privacy – A Review of Apple’s Bluetooth Low Energy Continuity Protocol.”
[6] Cäsar et al., “A Survey on Bluetooth Low Energy Security and Privacy.”
[7] Claverie and Lopes-Esteves, “Testing for Weak Key Management in Bluetooth Low Energy Implementations.”
[8] Claverie and Lopes-Esteves, “Testing for Weak Key Management in Bluetooth Low Energy Implementations.”
[9] Cäsar et al., “A Survey on Bluetooth Low Energy Security and Privacy.”
[10] Wang, “Securing Bluetooth Low Energy: A Literature Review.”
[11] Wang, “Securing Bluetooth Low Energy: A Literature Review.”
[12] Felch, “Machine-in-the-Middle (MitM) BLE Attack – Black Hills Information Security.Pdf.”
[13] Felch, “Machine-in-the-Middle (MitM) BLE Attack – Black Hills Information Security.Pdf.”
[14] Hensler and Tague, “Using Bluetooth Low Energy Spoofing to Dispute Device Details.”
[15] Hensler and Tague, “Using Bluetooth Low Energy Spoofing to Dispute Device Details.”
[16] Cäsar et al., “A Survey on Bluetooth Low Energy Security and Privacy.”
[17] Wang, “Securing Bluetooth Low Energy: A Literature Review.”
[18] Cauquil, “YOU’D BETTER SECURE YOUR BLE DEVICES OR WE’LL KICK YOUR BUTTS !”
[19] Hensler and Tague, “Using Bluetooth Low Energy Spoofing to Dispute Device Details.”
[20] Cäsar et al., “A Survey on Bluetooth Low Energy Security and Privacy.”
[21] Cäsar et al., “A Survey on Bluetooth Low Energy Security and Privacy.”
[22] Cäsar et al., “A Survey on Bluetooth Low Energy Security and Privacy.”
[23] Cäsar et al., “A Survey on Bluetooth Low Energy Security and Privacy.”
[24] Cäsar et al., “A Survey on Bluetooth Low Energy Security and Privacy.”
[25] Cauquil, “YOU’D BETTER SECURE YOUR BLE DEVICES OR WE’LL KICK YOUR BUTTS !”
[26] Cäsar et al., “A Survey on Bluetooth Low Energy Security and Privacy.”
[27] Cäsar et al., “A Survey on Bluetooth Low Energy Security and Privacy.”
[28] Cäsar et al., “A Survey on Bluetooth Low Energy Security and Privacy.”
[29] Wang, “Securing Bluetooth Low Energy: A Literature Review.”